What can you do to improve your company’s cybersecurity?

Now that the world is more than a year into the pandemic, companies must move beyond simply instituting stopgap measures and instead anticipate the “next normal.” Chief information security officers, CFOs, and cybersecurity teams must figure out how their workforces, customers, supply chains, and sector peers will work together to provide adequate cybersecurity. Here are five ways to start:
Enhance Vigilance Around Access: Zero Trust and Multifactor Authentication
Traditional IT network security is based on the castle-and-moat concept: Everyone inside the network is trusted by default, and it is difficult for those outside the network to obtain access. Cyberattacks that took place during the COVID-19 pandemic have exposed this strategy’s limitations. Companies should consider adopting a zero-trust strategy that maintains stringent access controls and does not trust any individual, device, or application by default—even those already inside the network perimeter. A zero-trust model requires identity verification and authorization for every person and device attempting to access resources on a private network. In 2019, Gartner predicted that by 2023, 60% of enterprises would move from VPNs to zero-trust initiatives.
Further, enterprises should mandate two-factor authentication for employees. Two-factor authentication requires a user to provide two different types of information to access an online account or IT system; typically, this includes a username/password pair (single-factor authentication) and another proof of identity, such as a code sent to an employee’s phone or email address.
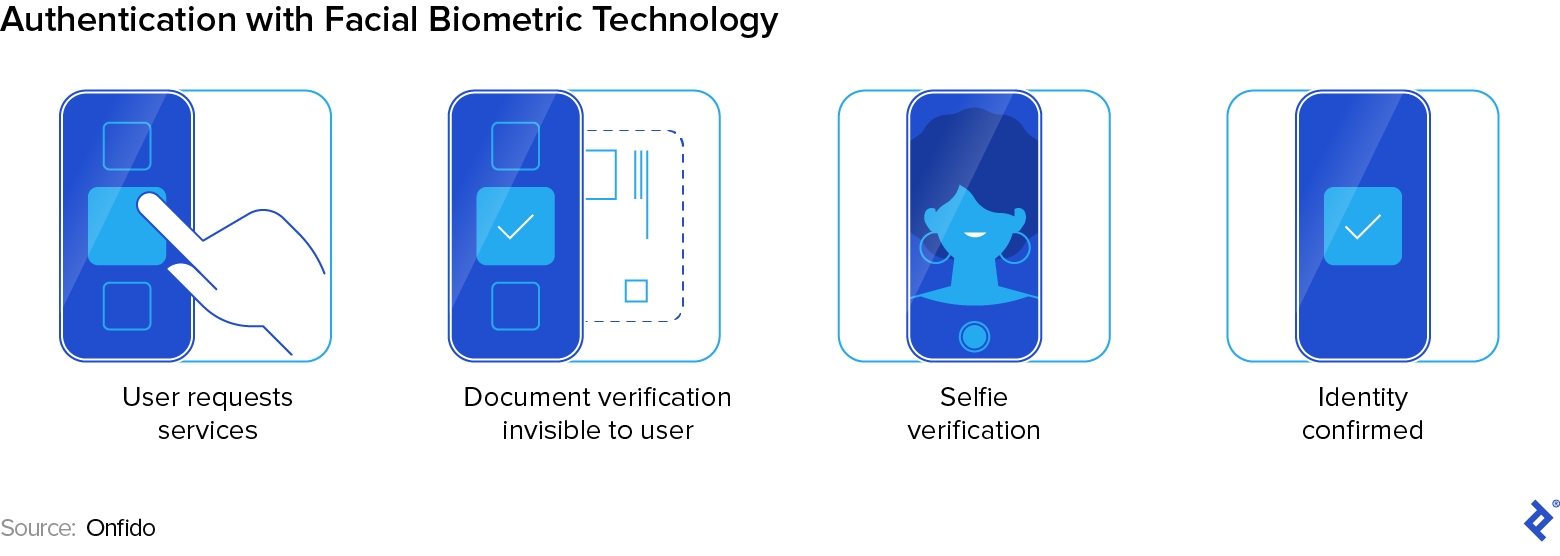
The World Economic Forum recommends that businesses also begin the transition toward biometric multifactor authentication using fingerprints, faces, typing behavior, or other factors to verify users’ identity. In contrast to companies that store their customers’ passwords on their servers, user biometrics are stored on the user device, and thus, there is no single data collection point for cyber criminals to access and the risk of online fraud and identity theft is greatly reduced. The global biometric system market size is projected to grow from $36.6 billion in 2020 to $68.6 billion by 2025.
Rethink Supply Chain and Third-party Risk
To bolster cybersecurity, organizations must examine their security tools and requirements for sharing and maintaining private information with vendors. Organizations should begin by reviewing all vendors and potential shadow third-party services; assign risk tiers to vendors, delineating those most critical to operations and having the greatest access to vital information; and then calibrate assessment scope correspondingly.
Enterprises should then update controls and access restrictions for third parties, and develop more robust data-loss controls. Organizations must also ensure that vendors that aren’t currently prepared for heightened cyber risk commit to developing cyber preparedness plans to safely handle information and interact with organizations’ corporate networks. Further, where possible, enterprises should integrate critical third-party logs into enterprise security monitoring and create alert systems for coordinated monitoring and response. Taking all these steps will help build cyber resilience across supply chains.
Develop and Enhance a Cloud Security Skill Set
As organizations move away from traditional on-premises cybersecurity solutions and toward cloud-centric architectures, they must learn to defend the cloud.
Cloud and container misconfiguration can be an issue because, in contrast to an on-premises network where only IT professionals can set up and deploy network infrastructure, in a cloud environment, far more people can do so. Attackers often leverage misconfigurations to access a network because they are easy to spot. Organizations can help manage misconfigurations by following Gartner’s Market Guide for Cloud Workload Protection Platforms to establish a baseline for assets connected to the network. (The full report is available for purchase here.) From there, organizations should monitor those assets for deviations and potentially employ automated defense measures to protect their systems against attacks.
As for network visibility, asset discovery tools provide device discovery and an awareness of not only what is in the network but also which assets are unprotected. These tools provide transparency into the relationships between assets, their usage, the network, and other devices, including which software modules are installed on the network.
Lastly, organizations can defend against unprotected cloud runtime environments for containerized workloads. When a device attempts to run an application, runtime environments act as a middleman between the application and the operating system.
Use Artificial Intelligence and Machine Learning
Although human security analysts already employ automation tools to extract the most urgent alerts from massive datasets and trigger humans to take action, artificial intelligence (AI) and machine learning (ML) tools are becoming increasingly sophisticated.
“We’re moving beyond algorithms that just look at your metrics and tell a human to do something about a certain outlier,” Splunk’s Vice President of Engineering and Head of Machine Learning, Ram Sriharsha, says in the company’s 2021 Data Security Report. “As a matter of scale, we need algorithms and automation that take action. In the security domain, we won’t just train models on past bad actors and behavior to identify new, similar behavior. We’ll see algorithms that just look at what’s happening—look at traffic, look at data—to identify bad patterns and take evasive action.”
Organizations should consider the use of self-learning, AI-based cybersecurity management systems. However, as AI/ML cybersecurity solutions develop, so do attackers. Using adversarial learning, bad actors glean enough about an AI/ML model to design ways of poisoning the system and rendering it ineffective for defense. Adversarial learning is akin to, say, tricking an autonomous vehicle into misunderstanding a stop sign. And according to Gartner research, 30% of all AI cyberattacks will leverage training-data poisoning, AI model theft, or adversarial samples to attack AI-powered systems through 2022. Yet despite these threats to AI/ML systems, a recent Microsoft survey revealed that 25 out of 28 businesses indicated they did not have the right tools in place to secure their AI/ML systems. Don’t be one of them.
Launch Interactive Employee Cybersecurity Training
Though seemingly simple, it is critical for organizations to enhance employee training around cybersecurity measures. Organizations should design role-based training programs and exercises to increase awareness around new cyber risks in a remote environment, including new threats, rules for approved device usage, and processes to report cyber incidents.
Management teams should also provide simulations and walk-throughs for cyberattack scenarios to actively engage employees. Management should also provide clear guidelines around required actions and when decisions should be escalated.
Lastly, employees should be reminded not to use public Wi-Fi networks or printers and not to store documents on home computers.
Staying Vigilant Against Cybersecurity Risks
To respond to escalating cyberattacks in the form of social engineering and supply chain attacks, and increasing shadow IT and vulnerable stopgap measures, enterprises should focus on adjusting to the “next normal.” That is, management must partner with cybersecurity teams to increase vigilance around access, rethink supply chain and third-party risks, develop cloud security skill sets, leverage AI and ML tools, and enhance interactive employee training. Creating secure environments for customers gives businesses a competitive advantage and builds trust and loyalty with their current and future customers.
More details https://www.toptal.com/finance/financial-forecasting/cybersecurity-landscape


